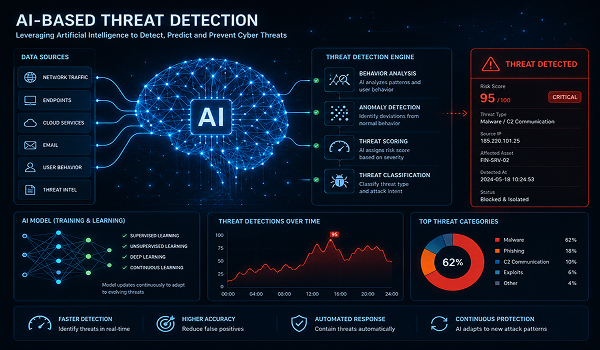
The Growing Importance of Business Security
Cyberattacks are no longer just IT problems; they are critical business risks that demand
strategic
attention. A single breach can disrupt operations, damage brand reputation, and lead to
significant
financial and regulatory consequences. Modern enterprises need more than fragmented security
tools; they
require a unified, intelligence-driven approach that protects every layer of their digital
ecosystem.
When you choose Polosoft, you gain a strategic partner committed to one goal: ensuring your
business
stays ahead of security attacks. From endpoint protection to compliance automation, our unified
security
platform delivers the resilience, visibility, and intelligence required for the digital age. The
future
of cybersecurity is proactive, integrated, and AI‑driven—and it’s available today with Polosoft.



 Engineering Services
Engineering Services

 AI &
Automation
AI &
Automation
 Cybersecurity
Cybersecurity
 Cloud Services
Cloud Services
 MVP Development
MVP Development
 Custom
Applications
Custom
Applications 




 Digital Branding
Digital Branding
 Industries
Industries



 Home
Home